دهن عود الكمبودي من رصاصي عطر لكلا الجنسين - او دي بارفان، 3 مل : Amazon.ae: الجمال والعناية الشخصية

بإختصار هذا عطرك المفضل يلي تبحث عنه ✌🏻 عطر سلطان العود مكونات العطر : العود و الزعفران السعر : ١٢ ريال ((( إطلب الآن ))) من المتجر… | Instagram

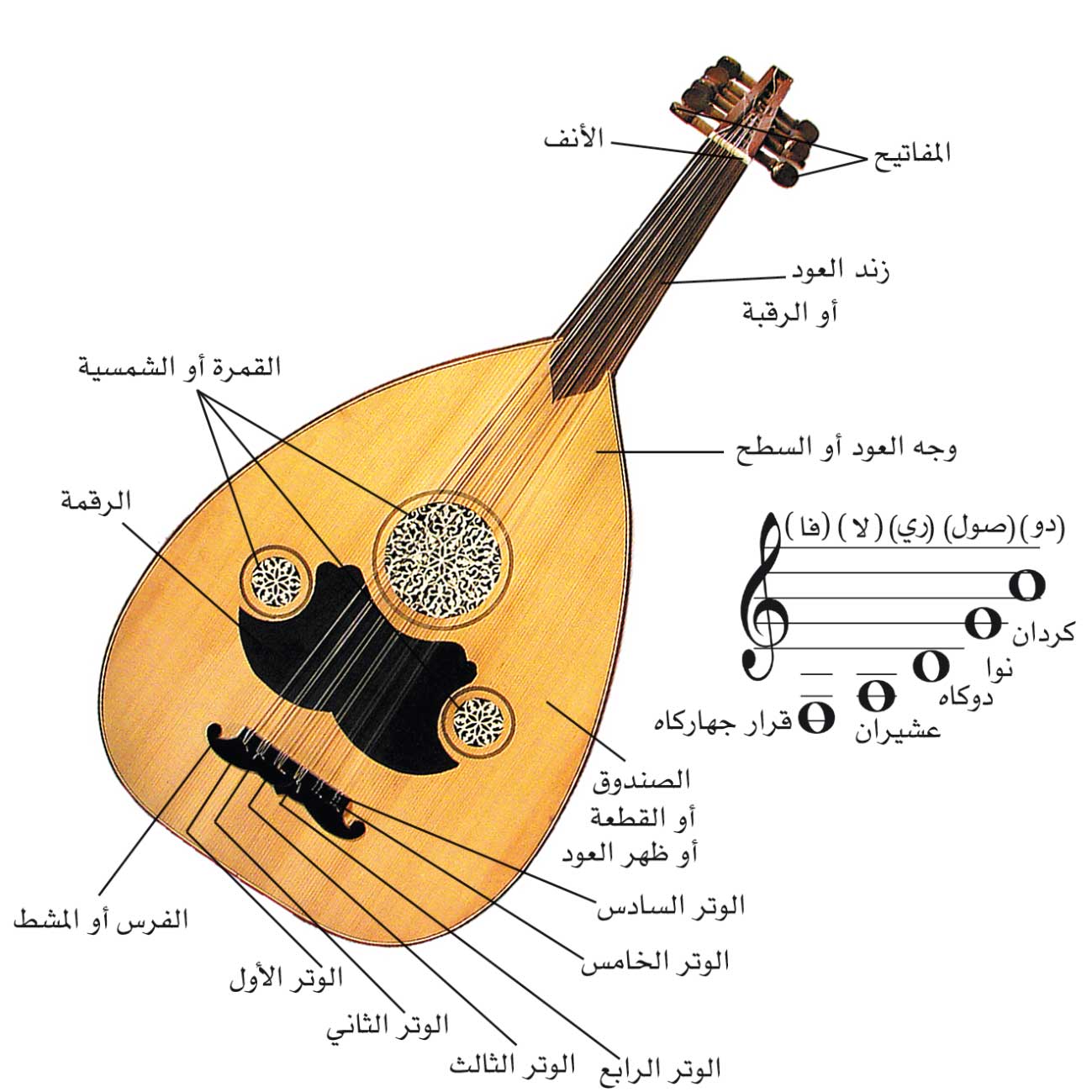
تعلم العود - مكونات العود: الصندوق (طهر العود، الصدر(قمرية)الفرس ،الرقبة ، الأنف ،المفاتيح ،الأوتار) يتألف العود من الأقسام التالية : -الصندوق المصوت و يسمى أيضا القصعة أو ظهر العود. -الصدر أو الوجه

مكونات مختارة بعناية وخبرة طويلة في صناعة أفخر أنواع العطور. اكتشف الآن مجموعتنا الجديدة من خلال موقعنا الإلكتروني، أو في… | Instagram

X Glossy للهدايا - 💙💠 عطر عود 24 ساعة من ارض الزعفران للرجال 💠 💙 ⛳ مكونات العطر : ✍تميز عود 24 ساعة من أرض الزعفران بانه أو دي بارفان مشهور ومميز

Perfume for you - #perfume_for_you# بكرات عود مكونات العطر Oud Satin Mood خشبي شرقي يحتوي على خلاصة العود الطبيعية القادمة من لاوس مع خلاصة الورد البلغاري و خلاصة الورد التركي المركزة و

هذا المنتج الكمبودي النقي المفعم بالطاقة "دهن العود" ممزوج مع مكونات نقية طبيعية من عائلة اكولارية لدهن العود. إنه للّذينَ يحبون الروائح… | Instagram